
Started from 08:13:06 PM UTC on May 7th, 2021, ValueDeFi’s multi-strategy WBNB vault was exploited due to an invalid share calculation exploit. In this post, we review the technical details of this issue step by step.
1. TL;DR
- At the time of the exploit, ValueDeFi’s multi-strategy WBNB vault had two live strategies: Alpaca Finance and CDO.Finance.
- An incorrect assumption in ValueDeFI’s regarding Alpaca’s Finance ibBNB price, led to the number of shares issued to be miscalculated, inflating the amount of VSafeVault BNB shares the attacker received when depositing BNB into the vault.
- The attacker was then able to redeem his inflated shares back for BNB, causing loss of funds in ValueDeFi’s BNB Vault.
- Only the funds in ValueDeFi were affected by this attack. Funds in Alpaca Finance were safe.
- A similar attacking vector happened on the Rari Capital exploit, by the same attacker on Ethereum (https://nipunp.medium.com/5-8-21-rari-capital-exploit-timeline-analysis-8beda31cbc1a).
2. Related BSC Addresses
- Attacker’s Wallet:
0xcb36b1ee0af68dce5578a487ff2da81282512233 - Attacker’s Malicious Token:
0x4269e4090FF9dFc99D8846eB0D42E67F01C3AC8b - Malicious Token-WBNB PCS LP: 0xbfa618f7b7078be3b00f5ccfb85907083efab9f0
- Alpaca Vault:
0xd7D069493685A581d27824Fc46EdA46B7EfC0063 - Alpaca PancakeswapV2Worker: 0x7Af938f0EFDD98Dc513109F6A7E85106D26E16c4
- Alpaca PancakeswapV2StrategyAddBaseTokenOnly:
0xE38EBFE8F314dcaD61d5aDCB29c1A26F41BEd0Be - Value VSafeVaultWBNB:
0xd4bbf439d3eab5155ca7c0537e583088fb4cfce8 - Value VSafeVaultController:
0x2b4f87d9d0a32a04b2d045fd5927cb57bedb076e - Value StrategyAlpacaWBNB:
0xb43410A271C71f2FDA2D1ED9C1165e924Be159D9
3. In-depth Technical Details
3.1. Abusing Alpaca Vault work() Function to Utilize Execution Flow
In Alpaca Finance, users can open a leveraged yield farming position using work() function, in which the pool can be selected dynamically using the farming token.
Attack Prerequisites:
- A token with a specially written
approve()function must be deployed
Attack Steps:
- The attacker called the
work()function of Alpaca’s WBNB Vault contract with malicious data encoded in the data variable, which was passed to thework()function of the worker contract (PancakeswapV2Worker).
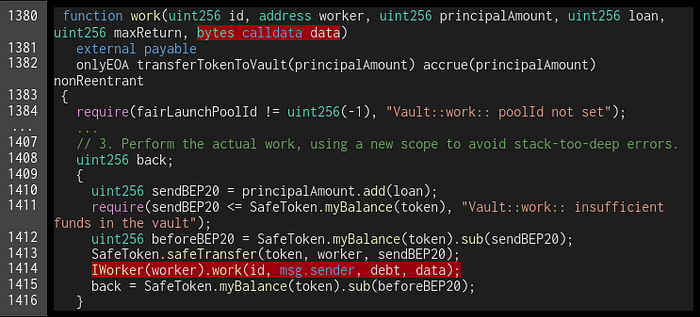
- In the worker contract (
PancakeswapV2Worker), the data was then decoded into two variables,stratandext.stratis the address of the strategy used, and the worker checked whether the address was an approved strategy contract, so this value could not be arbitrarily manipulated. Whileextvariable was passed further to theexecute()function in the decoded strategy contract.
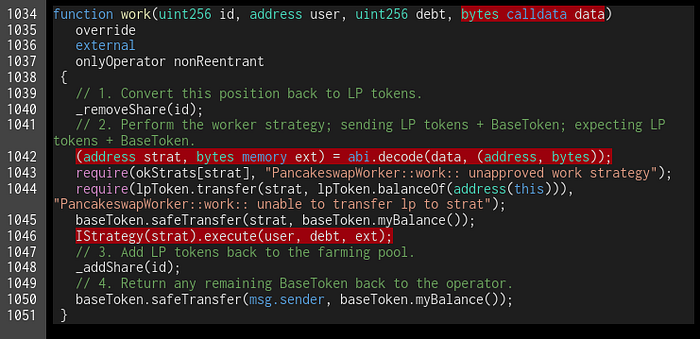
- In the strategy contract (
PancakeswapV2StrategyAddBaseTokenOnly), the data variable (extvariable in the worker contract) had a maliciousfarmingTokenaddress embedded. With the contract calling the maliciousapprove()function of the malicious token, the attacker used the execution flow to interact with theVSafeVaultWBNBcontract.
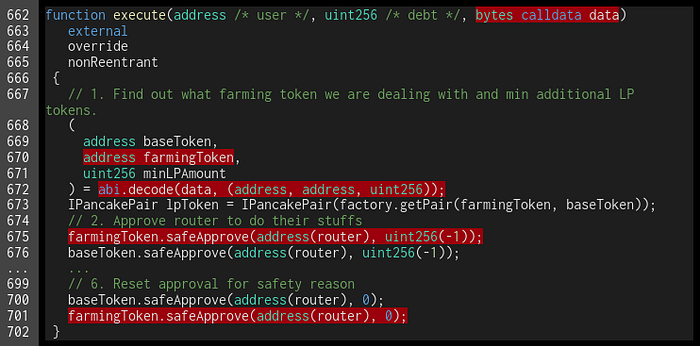
By using the steps above, the attacker utilized the execution flow of the work() function in Alpaca’s WBNB Vault contract as shown in the following screenshot. The marked transactions with the red box were executed by the malicious contract.
In this case, the cross-contract execution happened during the phase where the balance of the token inside the vault contract had been transferred to the worker, but before the debt value was updated.
Alpaca Finance’s smart contracts have security mechanisms in place that prevent reentrancy attacks, so the tokens inside Alpaca Vault contracts are safe from these types of attacks. However, Value’s integration of this Vault contract had a loophole that the attacker was able to exploit.
To sum up, the attacker called Alpaca’s WBNB Vault with a malicious input, allowing the attacker to execute functions in the ValueDeFi platform during the period when not all variables were fully updated, so the calculations on ValueDeFi were done incorrectly, which was the attacker’s target.
3.2. Invalid Share Calculation in Value’s vSafe Vault
ValueDeFi’s VSafeVaultWBNB contract is a multi-strategy vault that compounds users’ funds to multiple destinations by selecting the best strategy. However, with ValueDeFi’s incorrect assumption of the balance value in Alpaca Vault, the amount of shares were miscalculated, causing loss to the funds in Value’s vSafe Vault.
Attack Prerequisites:
- The current best strategy must be any pool other than Alpaca Vault
Attack Steps:
- In ValueDeFi’s
VSafeVaultWBNBcontract, tokens can be deposited into the vault using thedepositFor()function. This function checks whether the deposit cap is exceeded, gets the balance of the pool using thebalance()function, then passes the pool balance to the_deposit()function.
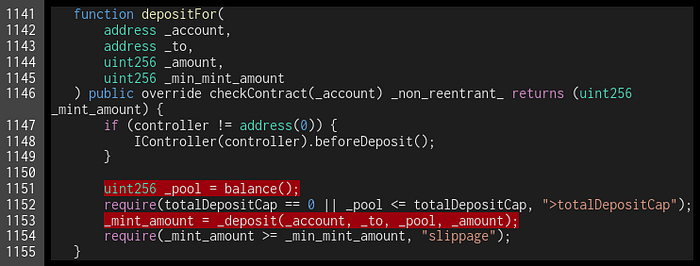
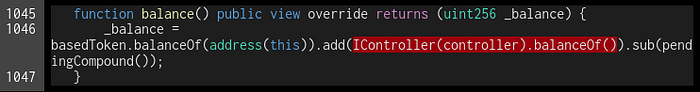
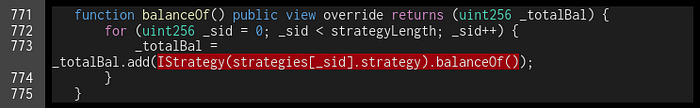
- The
balance()function calculates the sum of the base token in the vault contract and the balance of the token in each strategy pool. The sum is then deducted with the pending compound.
As the WBNB token balance of Alpaca Vault had been transferred to the Alpaca Worker, but the debt value was not yet updated, the value of the pool balance calculated was less than the actual value.
- The
_deposit()function then transferred the base token to be deposited to the contract, and calculated the amount of share to be minted from this deposit.
As the pool balance was improperly calculated to be lower than the actual amount, this resulted in a higher number of shares being minted.

In this case, with the miscalculated balance by ValueDeFi, the attacker was able to deposit WBNB and gained a larger amount of vSafeWBNB tokens than usual. This can be seen in the screenshot below:
In the next transaction, the attacker burned the vSafeWBNB tokens gained from the previous transaction and withdrew WBNB from VSafeVaultWBNB as shown in the screenshot below:
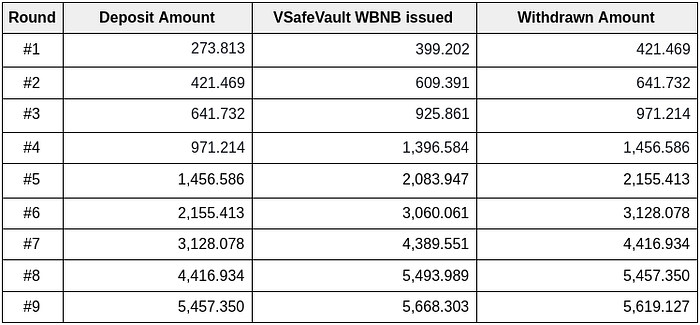
In this attack, the attacker deposited 1,456.58 WBNB to gain 2,083.95 vSafeWBNB tokens. Then withdrew 2,144.41 WBNB tokens by burning the vSafeWBNB tokens minted. From this transaction, the attacker gained 687.83 WBNB tokens from the VSafeVaultWBNB contract.
4. Attack Summary
The attacker repeated these steps 9 times. In total, the attacker gained 5345.314 WBNB from VSafeVaultWBNB contract as shown in the table below.
4.1. Tx Links
Round #1: Tx Link
Deposit, Withdraw
Round #2: Tx Link
Deposit, Withdraw
Round #3: Tx Link
Deposit, Withdraw
Round #4: Tx Link
Deposit, Withdraw
Round #5: Tx Link
Deposit, Withdraw
Round #6: Tx Link
Deposit, Withdraw
Round #7: Tx Link
Deposit, Withdraw
Round #8: Tx Link
Deposit, Withdraw
Round #9: Tx Link
Deposit, Withdraw
5. Actions taken by Alpaca Finance
Inspex worked with Alpaca Finance since we became aware of the attack on May 8th, 2021.
Alpaca Finance’s team communicated to us that the strategies were intentionally designed to act as a library that other protocols could utilize and integrate. This is a common open-source approach to dapp interoperability in DeFi. However, from this incident, we made a suggestion to Alpaca Finance to make changes to the contract permissions, in order to prevent similar attacks from occurring to other platforms that build off Alpaca’s protocol without authorization or proper oversight, and might make incorrect assumptions on certain parameters.
Together with Alpaca Finance, we worked out a solution and Alpaca Finance’s relevant contracts are now updated with the suggested adjustment applied. Strategy now only reads baseToken and farmingToken from the Worker contract, and only whitelisted workers can interact with the strategy.
6. Recommendations for ValueDeFi
To prevent this attack in future integration with any platform, the last known price of any asset should be kept as a reference. In case of an abnormal change of the price due to malicious manipulation, the transaction must be reverted or consider using an oracle to prevent this attack.
About Inspex

Inspex is formed by a team of cybersecurity experts highly experienced in various fields of cybersecurity. We provide blockchain and smart contract professional services at the highest quality to enhance the security of our clients and the overall blockchain ecosystem.
For any business inquiries, please contact us via Twitter, Telegram, contact@inspex.co
